What is Cyber Resilience?
As the world becomes increasingly reliant on technology, the internet, and cloud computing, the level of cyber crime occurring around the globe is also on the rise. Consequently, “cyber security,” a term used to describe defending data, networks and IT systems, from cyber attacks, has become a hot topic in the business world.
While cyber security is incredibly important, organizations are beginning to realize that they need to take their data protection strategies a step further. The term “cyber resilience” is becoming more prevalent, as a means of describing an organization’s ability to continue operating and to uphold the integrity of their data, even in the event of a breach. If “cyber security” is an organization’s ability to defend against a cyber attack or breach, “cyber resilience” is an organization’s ability to protect their data if a breach occurs, and to recover from the breach.
How Does Cyber Resilience Work?
Cyber resilience is all about having the right tools and processes in place, to adapt to and bounce back from a cyber attack. If your cyber security mechanisms fail, what’s your next line of defense?
For example, if an employee falls victim to a phishing scam and accidentally reveals their company credentials to a cyber criminal, will they be able to access the organization’s data and disrupt their daily business operations? If a hacker circumvents the cyber security barrier and infects the company’s database with ransomware, will their employees be able to keep working? Will the business be able to recover its files if they’re stolen?
These situations are where cyber resilience comes into play. There are several different tools and strategies that can be utilized to ensure an organization can survive a cyber attack. For example:
- Encryption: An encryption solution is an example of a tool that an organization could use to stay protected in the event of a breach or cyber attack. Encryption translates data into an unreadable format, to prevent unauthorized parties from reading it. If a hacker was able to bypass the organization’s outer defense, and access their data, they wouldn’t be able to read it because it’s encrypted. Only the members of the organization that hold the encryption keys are able to decrypt and read the data.
- Data Backups: Even if an organization has a cyber security strategy in place, there’s still always a possibility that a hacker will be able to get through. If they do, it’s important to also have a plan for recovering data, should it be corrupted or stolen. This is where backup and disaster recovery solutions come in handy. Backups play a crucial role in allowing businesses to recover from a cyber attack, and enabling them to restore their original data. By saving a copy of your data up in the cloud, at another physical location, or on another server, you are more likely to be able to recover that data if the original version is compromised.
In addition to implementing these specific tools (i.e. encryption, backups), organizations must also develop a “cyber resilience framework,” or a set of security standards for the entire business to abide by. They need to evaluate the strengths and weaknesses within their current data protection strategy, and figure out what additional steps they need to take to help them adequately withstand or recover from a cyber attack. A company that is truly “resilient” will have both of these components in play.
What Are the Benefits of Cyber Resilience?
Here are some of the benefits provided by adding cyber resilience to your data protection and security strategy:
Data Protection
![]() One of the most valuable benefits that implementing a cyber resilience strategy provides is added data security and protection. Breaches and cyber attacks are on the rise, and while cyber security solutions are helpful in keeping data guarded, they are by no means impenetrable. With cyber resilience, if a cyber criminal manages to get past your cyber security layer, they will be blocked by additional forms of protection. If they manage to get past those as well, you’ll be able to recover your corrupted or stolen data. Having extra precautions in place will give your organization added confidence and peace of mind.
One of the most valuable benefits that implementing a cyber resilience strategy provides is added data security and protection. Breaches and cyber attacks are on the rise, and while cyber security solutions are helpful in keeping data guarded, they are by no means impenetrable. With cyber resilience, if a cyber criminal manages to get past your cyber security layer, they will be blocked by additional forms of protection. If they manage to get past those as well, you’ll be able to recover your corrupted or stolen data. Having extra precautions in place will give your organization added confidence and peace of mind.
Loss Prevention
 A serious data breach can negatively impact a business in several different ways. Most important are the financial ramifications; according to a report from IBM and the Ponemon Institute, the average cost of a data breach in 2023 is $4.45 million. In addition to being incredibly expensive, breaches can also destroy an organization’s reputation and significantly impact employee productivity, making it difficult for companies to get back on their feet. By implementing a cyber resilience strategy, your organization will improve its overall security and be more likely to prevent a breach from occurring, or recover promptly if one does.
A serious data breach can negatively impact a business in several different ways. Most important are the financial ramifications; according to a report from IBM and the Ponemon Institute, the average cost of a data breach in 2023 is $4.45 million. In addition to being incredibly expensive, breaches can also destroy an organization’s reputation and significantly impact employee productivity, making it difficult for companies to get back on their feet. By implementing a cyber resilience strategy, your organization will improve its overall security and be more likely to prevent a breach from occurring, or recover promptly if one does.
Regulatory and Legal Compliance
![]() Nowadays, there are major regulations that exist across multiple industries and geographies, with the purpose of maintaining the security of clients’ personal, and often sensitive, data. Examples include: healthcare (HIPAA), financial services (PCI-DSS and GLBA), and IoT (NERC and FERC). Failure to comply with these regulations can result in a number of penalties, including fines, increased fees, and revocation of rights to interact with clients in given industries. Oftentimes, cyber resilience measures are necessary amongst these specific sectors, to meet compliance requirements and ensure the protection of confidential customer data.
Nowadays, there are major regulations that exist across multiple industries and geographies, with the purpose of maintaining the security of clients’ personal, and often sensitive, data. Examples include: healthcare (HIPAA), financial services (PCI-DSS and GLBA), and IoT (NERC and FERC). Failure to comply with these regulations can result in a number of penalties, including fines, increased fees, and revocation of rights to interact with clients in given industries. Oftentimes, cyber resilience measures are necessary amongst these specific sectors, to meet compliance requirements and ensure the protection of confidential customer data.
Cyber resilience is a dynamic and adaptive process that involves multiple layers of defense and recovery mechanisms. It acknowledges that cyber incidents are not a matter of “if” but “when,” and it seeks to minimize the impact of such incidents while maintaining the organization’s ability to function effectively.
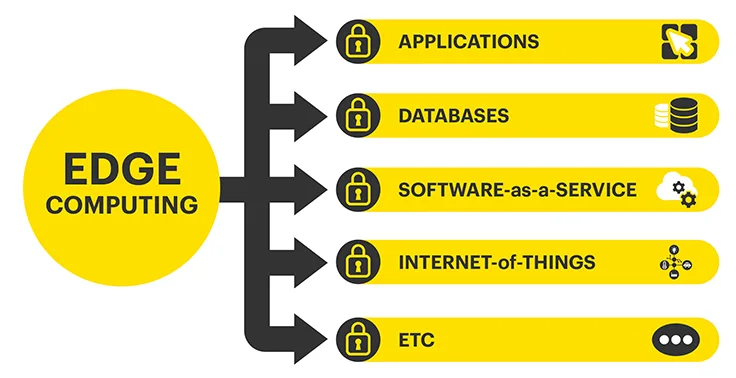
Cyber Resilience Framework and Edge Computing
Edge computing organizations face some unique challenges when it comes to data security. A retail chain, for example, may have hundreds of different store locations, each holding terabytes of sensitive information, and may not have the budget to deploy data security technology at each individual site. A remote office or manufacturing plant may not be physically secure, putting them at risk of having their IT equipment tampered with or stolen. Businesses with hundreds to thousands of IoT devices are vulnerable because they often manage and store users’ personal data and don’t have built-in data protection.
Edge computing environments are generally more susceptible to breaches. These types of organizations typically aren’t physically secure, store sensitive information that is targeted by cyber criminals, and they often have many locations to manage and secure, which can be expensive and complex.
It is for these reasons that edge computing sites can benefit from implementing cyber resilience strategies. If their cyber security tools happen to fail, they can rest assured that their sensitive data will still be safe, thanks to their additional layers of protection.
StorMagic offers solutions that are tailored specifically for the edge, and that allow edge organizations to remain secure and resilient in the face of cyber threats. Learn more about our products, SvSAN and SvKMS, and how they enable cyber resilience, in the sections below.
StorMagic SvSAN and Cyber Resilience
As mentioned above, encryption is an excellent tool for keeping data secure and protected, even in the event of an intrusion. While a cyber criminal may be able to get past an organization’s cyber security layer, encryption will keep them from reading the data on the other side. Only those who possess the encryption keys will be able to translate the data from ciphertext to plaintext.
SvSAN, StorMagic’s virtual SAN solution, possesses a data encryption feature, available as an addition to its base license. The feature delivers the most cost-effective encryption on the market for storing data in edge computing environments. The 100% software approach eliminates the need for operating system or hypervisor-level encryption and does not require any special hardware (self-encrypting drives). Organizations get a simple and inexpensive way to protect sensitive data at the edge, where servers aren’t typically located in secure datacenters.
SvSAN’s data encryption feature has been developed to provide ultra-secure FIPS 140-2 compliant encryption and the flexibility to work with any KMIP-compliant key manager, including StorMagic SvKMS. Visit our SvSAN Data Encryption page to learn more.
StorMagic SvKMS and Cyber Resilience
An encryption key management solution is another tool that should be incorporated into an organization’s cyber resilience strategy. Key management systems (KMS) secure an organization’s encryption keys, to prevent unauthorized individuals from accessing and corrupting sensitive data that has been protected through encryption.
StorMagic SvKMS enables secure and effective encryption key management, within any encryption workflow. It is a powerful key management solution that allows organizations to store keys anywhere — whether it be at the edge, in the datacenter, or cloud. It adapts to, and integrates with, any environment, to deliver flexible, robust, simple key management, all within a single platform, at a surprisingly low cost.
SvKMS eliminates the need for hardware security modules (HSMs) and uses a REST API for easy integrations into any workflow with custom key imports facilitating an easy transition from legacy solutions. It is FIPS 140-2 certified, allows advanced identification and access management through SAML 2.0, and can be configured as a single- or multi-tenanted solution.
SvKMS is a separately licensed product to SvSAN. Customers have the option to utilize SvKMS with SvSAN-based encryption, yet are free to utilize the key manager with any supported encryption application of their choice. SvKMS is KMIP-compliant, allowing compatibility with a wide range of solutions from different vendors, including Commvault, Nutanix, and MongoDB. SvKMS’s support also extends to a number of cloud applications, such as Google Cloud, Microsoft Azure, and Salesforce. Learn more about our different security technology integrations here.