BitLocker is attractive for encryption, but must be managed correctly
BitLocker is a built-in encryption feature for Windows, providing full volume AES 128-bit or 256-bit software encryption. It helps mitigate unauthorized data access by enhancing file and system protections and protects against theft of data on a lost or stolen computer, preventing unauthorized users from using hacking tools to get access to the data.
BitLocker also helps render data inaccessible when BitLocker-protected computers are decommissioned or recycled. As such, BitLocker is an attractive method of security for the individual computers used by an organization’s workforce.
However, when a Windows machine is encrypted with BitLocker, the backup encryption keys are often stored in an external device such as a USB key, relying on users to retain their backup key, taking control out of the hands of the IT administrator.
Secure, enterprise-grade key management for BitLocker
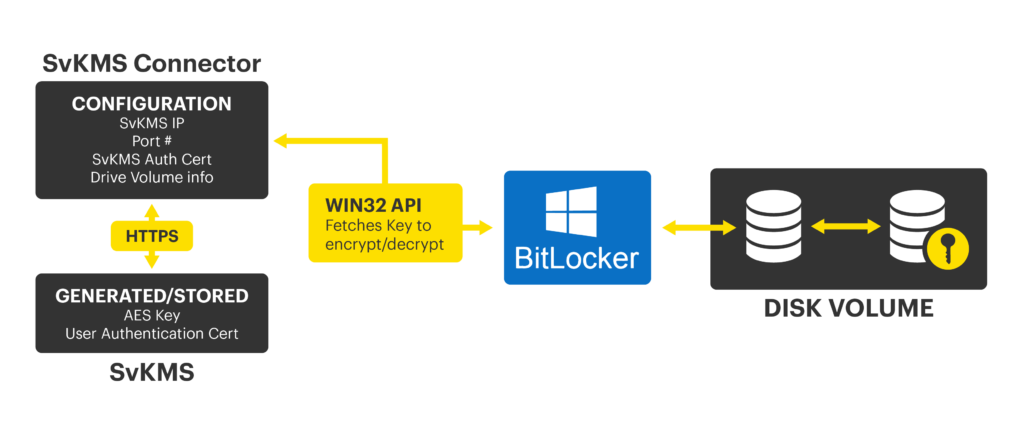
StorMagic SvKMS can provide an effective and secure enterprise-wide management console for BitLocker drive encryption by using external and secure encryption key protection instead of relying on external backup keys that may be lost by the user.
Integrating StorMagic SvKMS with BitLocker
As a separate key manager, StorMagic SvKMS can integrate with BitLocker and provide a centralized management tool for all BitLocker keys. This greatly reduces the complexity of managing all the keys within an organization, particularly when there are hundreds or thousands of computers to encrypt.
The BitLocker backup keys are protected through SvKMS, making it easy for administrators to encrypt Windows machines within their organization. When BitLocker encrypts a drive it creates a data encryption key (DEK) which typically has a vulnerable username and password authentication method. With SvKMS, the DEK is protected by an external key encryption key (KEK). The KEK is used to unlock the drive in a secure and centralized fashion.
For a full integration guide between SvKMS and BitLocker, please complete the form below.
BitLocker Integration Guide
Centralizing the management and protection of BitLocker backup keys is essential for any organization using them. StorMagic SvKMS can provide this interface with seamless integration.
For the complete step-by-step integration guide for configuring BitLocker and SvKMS, complete the form opposite.
By clicking download, you consent to allow StorMagic to store and process the personal information submitted and for StorMagic to contact you via telephone and email in relation to the content requested.
StorMagic is committed to protecting and respecting your privacy, and we’ll only use your personal information to provide the products and services you requested from us. You may unsubscribe from StorMagic marketing communications at any time. For more information on how to unsubscribe, our privacy practices, and how we are committed to protecting and respecting your privacy, please review our Data Protection Policy.
More information on StorMagic SvKMS
StorMagic SvKMS encryption key management goes much further than just providing simple KMIP or BYOK integration with leading encryption workloads. SvKMS enables organizations to manage all of their encryption keys, wherever they are located, within a secure, flexible management interface. Enterprise-grade features enable the management of the entire key lifecycle, from key creation to key destruction, and all at a surprisingly low cost.
