The news from the last few years is littered with stories about security breaches from electronic point-of-sale malware attacks on large US retailers, leaked online credit card payment details, sensitive defense documents being published, to celebrity private photos being stolen. Why is this happening, and are these organizations really following data encryption best practices?
The fact is that many of the breaches can be attributed to one or more of the following: unauthorized access (hacking), malware/viruses exploiting security holes from poor computer maintenance (patching), social engineering (email scamming), and in some cases hardware theft.
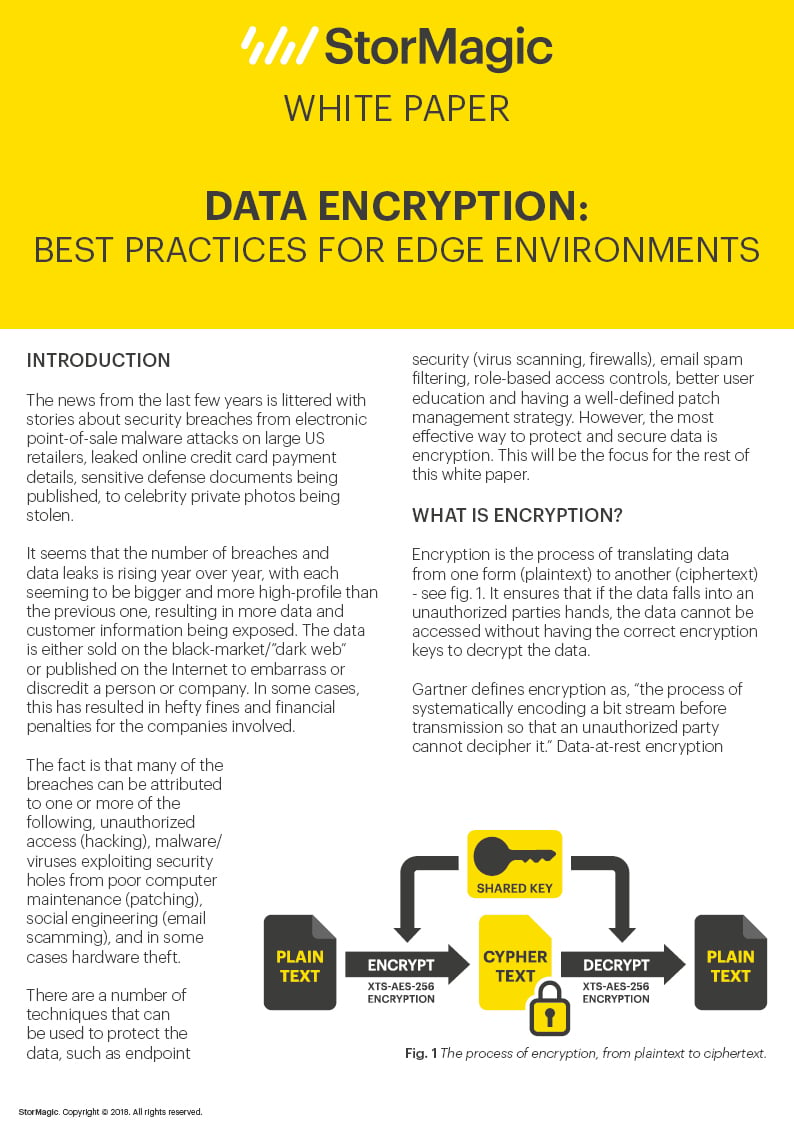
So what can be done to protect the data? There are a number of techniques that can be used to protect data, however the most effective way is through encryption.
This white paper explains encryption and sets out where it is appropriate and the data encryption best practices that can be applied to achieve data security. It also details key management systems and their requirements and the Key Management Interoperability Protocol (KMIP). It explains how SvSAN’s own data encryption feature can achieve cost-effective data security at the edge and concludes with a list of failure scenarios that SvSAN can tolerate without compromising data security.
Complete the adjacent form to read and download the full white paper.
By clicking download above, you consent to allow StorMagic to store and process the personal information submitted and for StorMagic to contact you via telephone and email in relation to the content requested.
StorMagic is committed to protecting and respecting your privacy, and we’ll only use your personal information to provide the products and services you requested from us. You may unsubscribe from StorMagic marketing communications at any time. For more information on how to unsubscribe, our privacy practices, and how we are committed to protecting and respecting your privacy, please review our Data Protection Policy.