Control your own encryption keys in Google Cloud
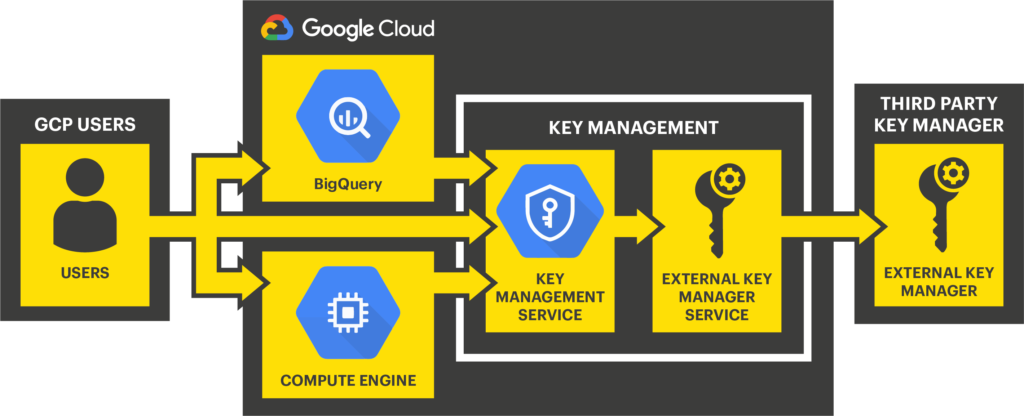
StorMagic SvKMS is fully integrated with server side encryption for Google Cloud Platform (GCP). This provides organizations with a robust, secure third party key manager that can safely handle keys for encryption workloads in Google Cloud. Rather than allowing Google Cloud to control both the encryption and the keys, SvKMS allows organizations to follow the key management best practice of separating lock and key, whereby the encryption enabled in the cloud service is separated from the digital key which is stored in an alternate location. Integrating SvKMS with Google Cloud is done through the External Key Manager Program.
Google Cloud External Key Management Program
Organizations can utilize the Google Cloud External Key Management (EKM) Program with StorMagic SvKMS. With Cloud EKM, Google Cloud customers use keys managed within a supported external key management partner to protect data within Google Cloud. Customers can protect data at rest in BigQuery or Compute Engine persistent storage, or by calling the Cloud Key Management Service API directly. In this instance SvKMS acts as the external key manager and Google provides the data encryption key (DEK). The benefits include:
- Key provenance: Users control the location and distribution of their externally-managed keys. Externally-managed keys are never cached or stored within Google Cloud. Instead, Cloud EKM communicates directly with SvKMS for each request.
- Access control: Users manage access to their externally-managed keys. Before customers can use an externally-managed key to encrypt or decrypt data in Google Cloud, users must grant the Google Cloud project access to use the key. Users can revoke this access at any time.
- Centralized key management: Users can manage their keys and access policies from a single location and user interface, whether the data they protect resides in the cloud or on-prem.
In all cases, the key resides on the external system, and is never sent to Google.
Google Cloud EKM Integration Guide
Separate key management from encryption within your Google Cloud instance through the use of a third party key manager such as StorMagic SvKMS. Our comprehensive integration guide demonstrates how it is done.
For the complete step-by-step integration guide for configuring Google Cloud EKM and SvKMS, complete the form opposite.
By clicking download, you consent to allow StorMagic to store and process the personal information submitted and for StorMagic to contact you via telephone and email in relation to the content requested. StorMagic is committed to protecting and respecting your privacy, and we’ll only use your personal information to provide the products and services you requested from us. You may unsubscribe from StorMagic marketing communications at any time. For more information on how to unsubscribe, our privacy practices, and how we are committed to protecting and respecting your privacy, please review our Data Protection Policy.
More information on StorMagic SvKMS
StorMagic SvKMS encryption key management goes much further than just providing simple KMIP or BYOK integration with leading encryption workloads. SvKMS enables organizations to manage all of their encryption keys, wherever they are located, within a secure, flexible management interface. Enterprise-grade features enable the management of the entire key lifecycle, from key creation to key destruction, and all at a surprisingly low cost.
