What is Encryption Key Management?
Encryption key management refers to the process of creating, using, storing, exchanging, archiving, discarding, and replacing cryptographic keys in an encryption system. Its purpose is to secure an organization’s keys, and to prevent cyber criminals or unauthorized individuals from accessing and corrupting sensitive data that has been protected through encryption.
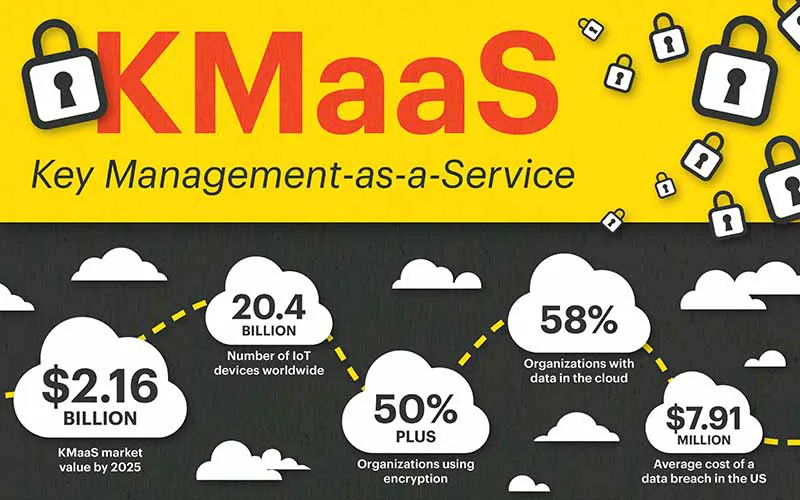
Businesses today are creating and storing huge amounts of valuable data, and keeping that data protected is a top priority. Security breaches, high-profile data losses, and regulatory requirements have all contributed to the increased implementation of encryption, resulting in the need to handle hundreds to thousands of cryptographic keys. Key management systems (KMS) are essential in helping organizations manage and maintain those keys, safely, securely, and efficiently.
How Does Key Management Work?
Encryption helps protect user data by encoding files through a complex algorithm and making them unreadable. This unreadable data is called ciphertext. Only members of an organization that have access to the encryption key(s) can translate the files back to plaintext to make them readable.
There are two different types of cryptographic algorithms – symmetric and asymmetric. A symmetric (private key) algorithm consists of a single key, that is only distributed amongst trusted members of an organization that are allowed access to sensitive data. These members use that key to both encrypt and decrypt information. An asymmetric algorithm, also known as public key cryptography, consists of two different keys – a private key and a public key. The private key is kept secret and only accessible by authorized users to decrypt ciphertext, while the public key is freely shared to allow anyone to encrypt a plaintext. A KMS is responsible for maintaining encryption keys – consolidating them into one location and keeping them from getting lost, corrupted, or accessed by an unauthorized individual. It also manages the key management lifecycle, filtering encryption keys through different stages (i.e. creation, rotation, archival, deletion).
What Are the Benefits of Encryption Key Management?
Data Protection
The ultimate goal of encryption and key management is to secure data from unauthorized access and corruption. Having an effective key management solution in place ensures that sensitive information is kept private and gives businesses peace of mind, knowing that their data is always protected. It provides organizations the control to be selective when granting authorization — allowing certain personnel and identities (applications, devices, etc.) to access their keys and data, but not others. This prevents valuable information from falling into the wrong hands.
Ease of Management
As companies grow, so does their data — and so does the number of encryption keys they have to manage to keep their data secure. Having a proper KMS in place simplifies complex operations by consolidating encryption resources into one location, and enabling automation and optimization of encryption processes. It also helps streamline encryption key lifecycle management, ensuring keys are updated, stored, and rotated as needed to meet various security policies. An effective key management solution is simple to use, and can be operated by nearly any IT professional, regardless of skill set or experience.
Accountability & Auditability
A robust key management system provides logs and audit trails, allowing organizations to track key usage and changes. This helps in accountability, monitoring, and forensic analysis in case of security incidents. By reviewing audit logs, organizations can ensure that encryption key management practices align with established policies, and any deviations are promptly addressed. In addition to aiding in technical analysis, well-maintained audit logs can serve as documentation in legal and compliance matters. They provide evidence of security measures taken, adherence to policies, and due diligence in protecting sensitive information.
Compliance
One of the biggest factors influencing organizations to implement encryption within their IT environments is compliance. Compliance standards and regulations vary between industries, and require different procedures and levels of protection. If a business doesn’t have proper protection in place, they can be fined significantly. Encryption key management is like insurance, providing that level of protection a business needs to ensure sensitive data won’t be compromised, and confirming that the necessary precautions have been taken to keep data safe.
Beyond Data Encryption
The Need for an Enterprise Key Management System
Encryption Key Management Best Practices
Effective key management helps protect data from unauthorized access and ensures the confidentiality and integrity of information. Keep the following best practices in mind when setting up a robust key management infrastructure.
- Centralized Key Management
Use a centralized key management system to maintain control over all encryption keys. Centralization helps in enforcing consistent policies and ensures better visibility and auditing capabilities. - Key Generation
Use a strong, secure, and random key generation process. Keys should be of sufficient length to resist brute-force attacks. Cryptographically secure random number generators should be employed for key generation. - Key Storage
Safeguard keys with strong access controls. Use hardware security modules (HSMs) or secure key vaults to protect keys from unauthorized access. Avoid storing keys with the data they encrypt. - Key Distribution
Establish secure channels for distributing encryption keys to authorized parties. Avoid using insecure methods such as email or unencrypted connections. Consider the use of secure key exchange protocols. - Key Rotation
Implement a key rotation policy to periodically change encryption keys. This limits the exposure of a single key and helps mitigate the impact of a compromised key. Ensure a smooth transition during key rotation to prevent data loss. - Key Revocation
Develop a key revocation process to promptly deactivate and replace compromised or suspected compromised keys. This is crucial for responding to security incidents and preventing unauthorized access. - Monitoring and Auditing
Implement monitoring and auditing mechanisms to track key usage and detect any suspicious activities. Regularly review logs and audit trails to ensure compliance and identify potential security issues. - Key Lifecycle Management
Define and implement a comprehensive key lifecycle management process, including key generation, distribution, usage, rotation, and retirement. This ensures that keys are managed consistently and securely throughout their entire lifecycle. - Key Metadata
Associate metadata with keys to provide additional context and information about their purpose, usage, and associated assets. This metadata can be useful for auditing, tracking, and understanding the role of each key. - Security Training
Educate personnel involved in key management about best practices, security policies, and potential threats. Security awareness training helps prevent human errors and ensures that key management practices are followed diligently. - Regular Security Assessments
Conduct regular security assessments and reviews of the key management infrastructure. This includes vulnerability assessments, penetration testing, and audits to identify and address potential weaknesses. - Compliance
Ensure that key management practices align with relevant industry regulations and standards. Compliance with standards such as PCI DSS, HIPAA, or GDPR may have specific requirements for key management.
By following these best practices, organizations can establish a robust encryption key management framework that enhances the overall security of their data.
Key Management and Edge Computing
Edge computing environments can often be defined by a few common characteristics: dispersed or distributed data processing (i.e. remote/branch offices and IoT technology), harsh conditions (i.e. manufacturing plants, oil rigs, wind farms), and limited resources (i.e. space, energy, IT staff).
Given these particular circumstances, implementing key management within edge computing environments makes sense for a few different reasons.
For one, edge computing data is often processed in environments that aren’t physically secure, such as within a closet of a retail store or back room of a manufacturing plant, which leaves edge sites more susceptible to breaches. Having an encryption key management solution in place provides an additional layer of protection, to keep data from being stolen or compromised.
Edge sites are also often producing and managing large amounts of personal identifiable information (PII) that is sensitive and must be kept private. They must follow strict regulations and guidelines to keep that data protected, and need to implement encryption key management to remain compliant.
Encryption key management is incredibly relevant for edge organizations managing data flow from IoT sensors and devices, as well. That data can be very sensitive and therefore may require proper protection protocols in place to keep it safe.
Interested in learning more about what defines an ‘edge’ environment? Explore our Beginner’s Guide on Edge Computing.
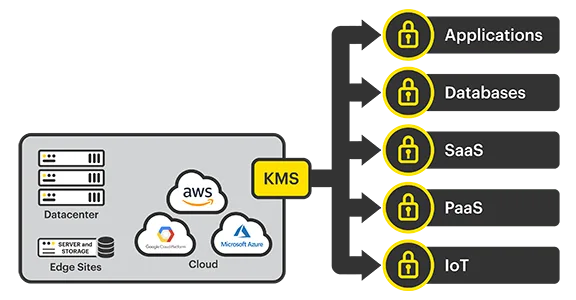
SvKMS and Key Management
StorMagic SvKMS is a powerful encryption key management solution that adapts to any environment. It delivers flexible, robust, simple key management, all within a single platform, at a surprisingly low cost. Learn more about the benefits of implementing StorMagic SvKMS below.